And now for something completely different… Many enterprises have multiple Secure Access (SA) or MAG appliances distributed globally to provide better remote access experiences to users all around the world. This post will discuss the need for a configuration push option, as well as describe how to perform said push.
The Juniper SA has been around for many years, and recently I had the experience of configuring a global VPN network for a client. The biggest issue to tackle was keeping configurations in sync across all the SA/MAG Appliances. In smaller enterprises it was trivial to cluster two SA/MAG appliances together to share configurations to not only provide High Availability (HA), but the clustering protocol would sync the configurations between nodes as well. However this is not possible when there are ten nodes are distributed around the world. Simply put, the SA/MAG’s clustering ability is limited to up to 4 nodes in the SA4500/SM160 modules and 8 nodes in the SA6500/SM360 modules. Moreover the clustering protocol is limited to low-latency environments which may prevent a node in the US from synching correctly with a node in China. Because of this limitation (and partially my laziness) I had to come up with an alternative to sync the node configurations.
In light of these limits Juniper has provided a different alternative – Configuration Push. The Configuration Push utilizes a method to copy the XML configuration between nodes without needing a clustering protocol or a manual upload. A single appliance can push its configuration to eight other appliances (known as Targets) at a time with click of a single button. In addition, the push utilizes HTTPS for communication which is usually permitted in many enterprises these days.
There are some slight restrictions in performing a push, however, and many of them are listed on Juniper’s Website such as:
- The Push Source and Targets must be running the same IVE OS version and build
- Pushes between standalone and clustered nodes are not supported; however many elements (role mappings, auth servers) can be pushed between them
- AD Authentication servers require all nodes to have a unique hostname when joined to the domain (yet another reason not to use AD Auth if at all possible); the push may override this setting
- The Push Source must use the internal or management port, but can connect to all ports of the Targets
- Network Settings, IVS configuration, and Licensing are not supported by the config push
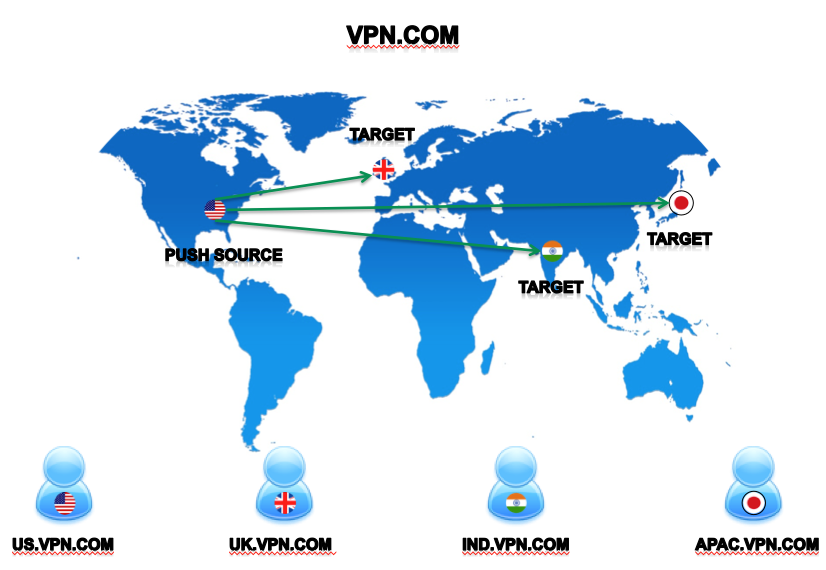
So with that in mind, let us begin a configuration push! Below is the topology we will use:
Assuming that the role is already created, we can proceed with the push. The first step is to create the push targets. In the Admin Configuration, navigate to Maintenance > Push Config > Targets and click on the New Target button:
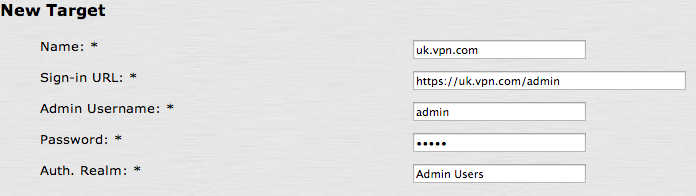
Here we will need to set the following parameters:
- Friendly Name of the Target
- Sign-In URL of the Target
- Admin Username
- Admin Password
- Authentication Realm the use will log in to
One thing to note here is that the Admin Username, Password, and Realm can be edited after the Target is saved. If the URL or name is incorrect then you must delete the Target and start over.
Once the Targets are defined then we can proceed with the configuration push. When performing a push configuration the important thing to keep in mind is that the push will need all elements pushed or else the push will fail. As an example if a new Role is created, mapped to a new security group inside a Realm then you will need to push the following elements:
- The Authentication Server
- The Authentication Realm
- The User Role
- The Resource Profile (if applicable)
- The Resource Policies (if new ones are created or modified)
First, navigate to Maintenance > Push Config > Push Configuration. Now you will have the option of pushing the entire configuration or just selected configuration; in this case we will only push a select configuration. To push our Role, Realm, and Auth configuration we will need to select the following:
- Sign-In Settings > Authentication Servers: Authentication Server
- Authentication Realms > User Realms: Users Realm
- Roles > User Roles: All User Roles
- Resource Policies: All Resource Policies
Next we will select all targets under the Under the Push Configuration and ensure that the Overwrite Duplicate Settings:

From here press the Push Configuration button and review the Results tab located at Maintenance > Push Config > Results to ensure that the push completes successfully across all nodes. You may need to refresh this page several times until you see the following:

Please feel free to leave comments or suggestions below!
