I recently learned a new trick from JTAC to test rewriting issues through Content Intermediation Engine without affecting production traffic. This can be used to test new code releases, or change parameters (ACL, rewriting filters, cross-domain access, etc.) on a lab SA and still be able to provide full access to TAC for additional troubleshooting.
The basic idea is to set up a JSAM role on the production SA, and connect via a proxying server (I have had good luck with the program CCProxy – it’s free for up to three users). From there, point a test SA (the Demonstration and Training Edition SA is perfect for this!) to the proxying server via a web bookmark. Lastly, use a client PC to connect to the lab SA to perform your tests. A diagram of the layout is shown below:

So let’s begin!
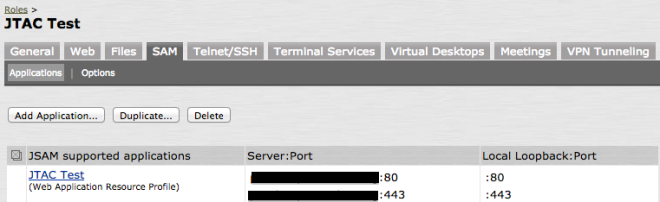
On the Production SA, create a JSAM access resource that points to the web resource:
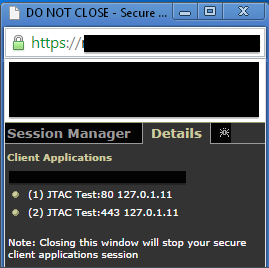
Connect to the customer’s SA and load JSAM, and take note of the localhost address being used (in the session manager window, click on Details to see the address):
From here, configure CCProxy to send traffic to that address (in this case, it’s 127.0.1.11) by clicking on the Configuration Button:

In your test SA, create a resource to point to your proxy server instead of the main server:

From there, log in as a user on the Test SA, and try and access the resource:


Success! You can confirm the connection in the logs in CCProxy by clicking the Monitor button:

Feel free to make adjustments in the test SA to try out new resource policies, code versions or even set up a passthrough proxy. Hope this tip helps someone!

